Bug Bounty Tips: Unveiling Vulnerabilities in IoT Firmware
This week’s bug bounty tip comes from Eslam Kamal from Cairo, Egypt. Eslam dives into IoT pentesting, focusing on firmware, software, and applications can lead to uncovering crucial vulnerabilities. Here’s a breakdown of effective steps and considerations to successfully map out attack surfaces and identify weaknesses in IoT firmware:
1. Attack Surface Mapping
Begin with comprehensively mapping potential entry points for attackers within the IoT solution. Create an architecture diagram that visually captures the device’s structure from a pentester’s perspective. This forms the foundation for prioritizing tests and understanding the system’s overall architecture.
2. Research and Information Gathering
Thoroughly gather intelligence about the target device. Explore documentation, online resources, prior research, and available CVEs to build a comprehensive understanding of the device’s characteristics, functionalities, and known vulnerabilities.
3. Firmware Analysis
Firmware is a treasure trove of information and vulnerabilities. Obtain the firmware binary through various means: online resources, physical access, or OTA updates. Use tools like “Binwalk” to extract the file system from the binary image. To install “Binwalk” on Kali Linux, use the following command:
sudo apt install binwalk
Once you have the firmware binary, extract it using the following command:
sudo binwalk -Me –dd=".*" {product_firmware.bin} --run-as=root
Gain insights into crucial firmware components such as bootloader, kernel, and file system.
4. Reverse Engineering
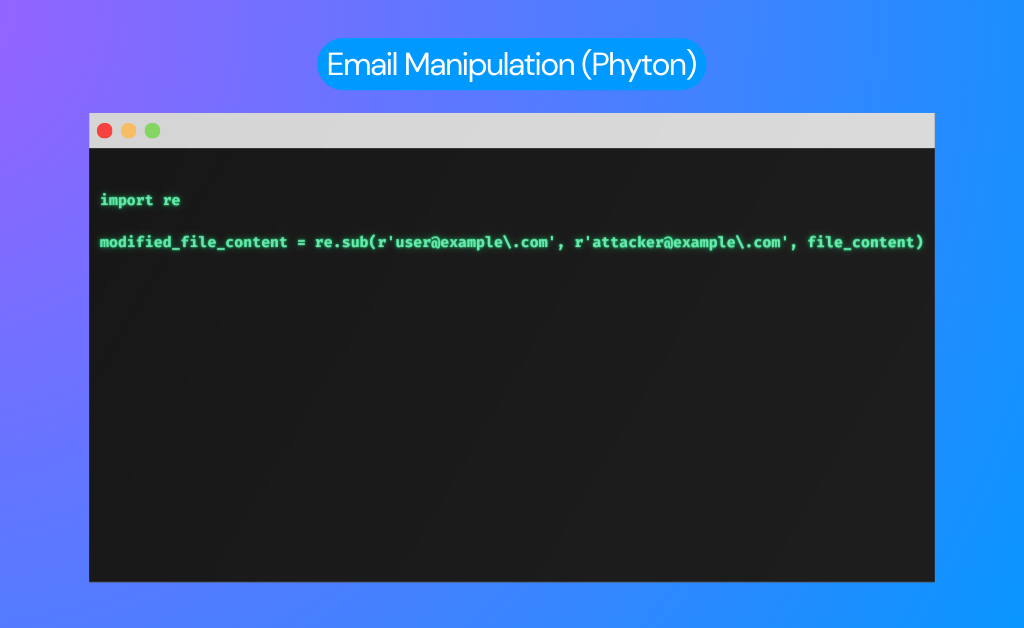
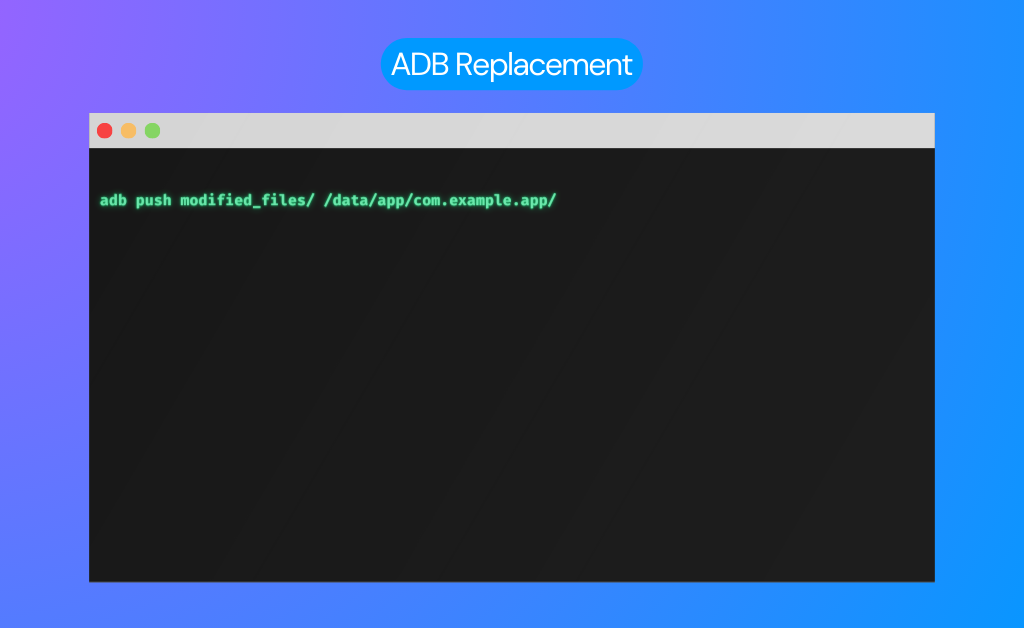
Apply traditional pentesting techniques to firmware and software components. Reverse engineer binaries, mobile applications, and cloud components to uncover secrets and vulnerabilities. Pay special attention to communication APIs to understand interactions between different IoT components and communication protocols.
5. Mobile Applications and Web Interfaces
Examine mobile applications and web-based dashboards that control the IoT device. Probe for vulnerabilities that may reveal sensitive information or unauthorized access. Exploit insecure network interfaces or outdated software versions for potential entry points.
6. Vulnerabilities in Embedded Devices
Focus on vulnerabilities unique to embedded devices. Explore avenues like exposed serial ports, insecure authentication mechanisms, firmware extraction through JTAG or Flash chips, external media-based attacks, power analysis, and side channel attacks. These avenues can expose critical security gaps.
Thank you for Reading
Check out Eslam Kamal‘s blog for more articles like this one. Access here.
Interested in getting featured on BugBounter’s social medias with your bug bounty tip? Join the BugBounter Community today, and reach out to us with your nickname and bug bounty tip.